Reporting and Deliverables
Executive Summary
An appendix with supporting documentation and diagrams
Identification of discovered security vulnerabilities with severity rankings…
Project Management
Own It Inc provide project management services in conjunction with their Information Security projects or they can work within your project management framework and provide your PM’s with assistance in initial scoping, detailed…
read moreNetwork Assessment
Inventory of all WAN/LAN active network devices
Internet, VPN and overall perimeter review
Firewall and gateway structure
Server Assessment
Document & Audit internal facing servers, providing software/hardware audits
Determine Patch/Vulnerability status of internal facing servers
Prioritization of servers based on risk
Desktop Assessment
Document & Audit desktops, providing software/hardware audits
Determine Patch/Vulnerability status of desktops
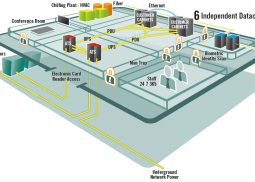
Physical Environment Assessment
Review of physical security controls
Perimeter
Parking and vehicular controls
Loading bays
Facilities Assessment
Power conditioning to include utilities, switch gear, UPS and generator
HVAC systems
Cable Plant (Physical Layer)
Heat, Smoke, Fire & Gas monitoring systems
Documentation, Policies and Procedures Assessment
Physical security
Business Continuity/Disaster recovery
Policy Review
Test results review
Procedure review
Vendor Management
Third Party Vendor Risk Management Assessment
Review of security policies and procedures
Human Resource Security
Risk and Asset Management
Incident Management
Social Engineering Assessment
Building access
Telephone social engineering
Employee awareness interviews
Email phishing
Application Penetration Assessment
Own It Inc provides application penetration testing to determine your application security weaknesses using real world attacks in authenticated and unauthenticated modes.
read more